Survive Fraud: The ID Verification Method Everyone Overlooks
In a digital landscape where trust is increasingly fragile, fraud detection is no longer optional—it’s essential. As online interactions grow, so do sophisticated schemes designed to exploit weak verification systems. Amid rising concerns, a foundational yet underappreciated strategy is quietly emerging: Survive Fraud: The ID Verification Method Everyone Overlooks. Hidden Rules Of ID Verification You Must Know To Avoid Blocked Access This approach centers on leveraging trusted identity checks—not just as a compliance hurdle, but as a proactive shield against deception. Whether you manage digital platforms, protect consumer data, or simply seek safer online experiences, understanding this method is key to staying ahead.
Why Survive Fraud: The ID Verification Method Everyone Overlooks Is Gaining Momentum in the US
The U.S. digital economy faces growing pressure to verify user identities reliably. With e-commerce, financial services, and social platforms expanding rapidly, fraud tactics have evolved beyond outdated passwords and basic login checks. Hidden Rules Of ID Verification You Must Know To Avoid Blocked Access Cybercriminals now use synthetic identities, deepfakes, and stolen credentials to bypass conventional systems. In response, responsible organizations are shifting focus to robust, layered verification—not just to meet regulations, but to protect both users and business integrity.
What’s overlooked in this shift is a simple but powerful principle: identity verification isn’t one-size-fits-all. Many rely on biometrics or third-party databases, yet fail to integrate basic, cost-effective layers that significantly reduce risk. This is where Survive Fraud: The ID Verification Method Everyone Overlooks becomes essential. Hidden Rules Of ID Verification You Must Know To Avoid Blocked Access It emphasizes using recognizable, scalable checks that fit seamlessly into user flows while building resistance to common fraud vectors.
How Survive Fraud: The ID Verification Method Actually Works
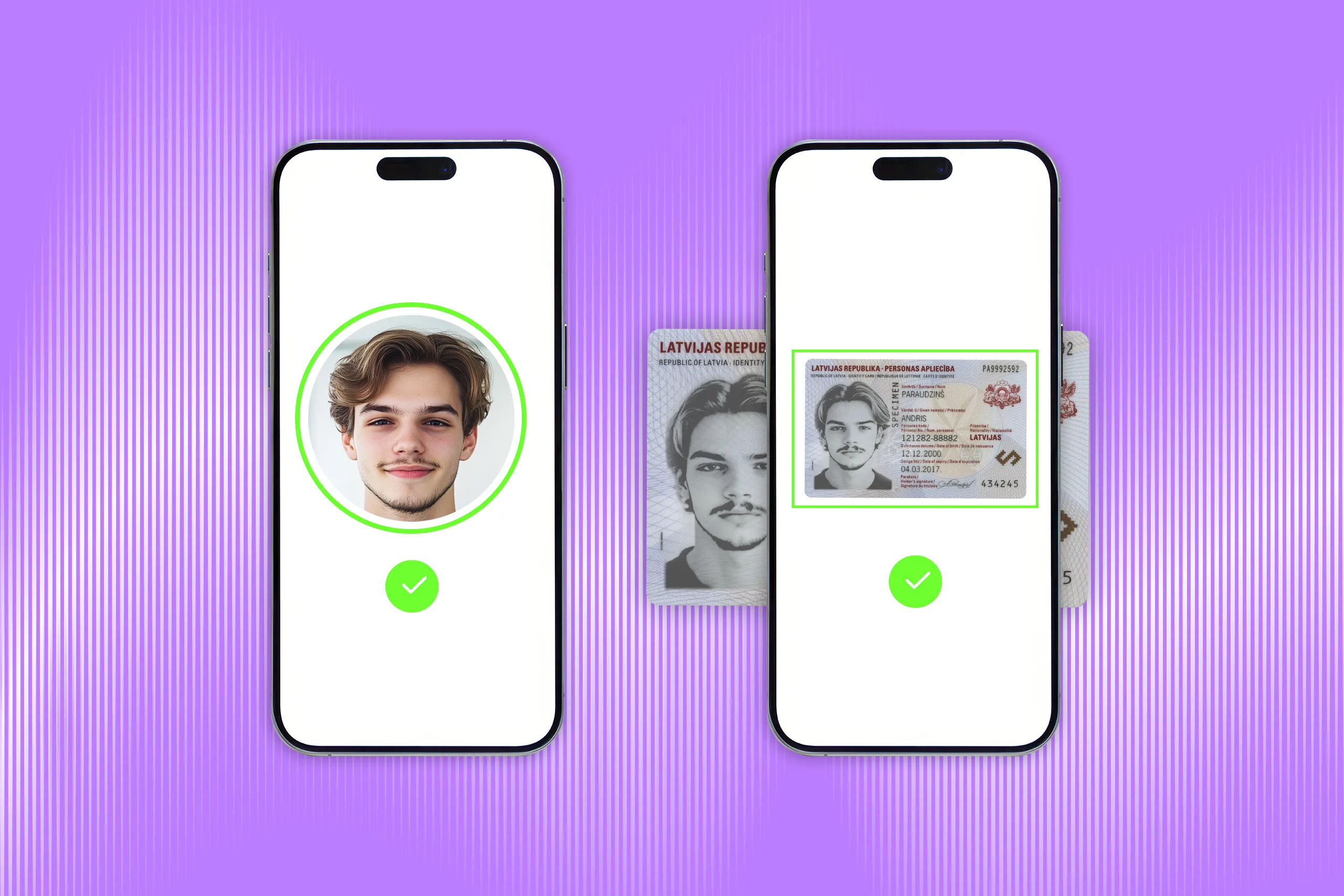
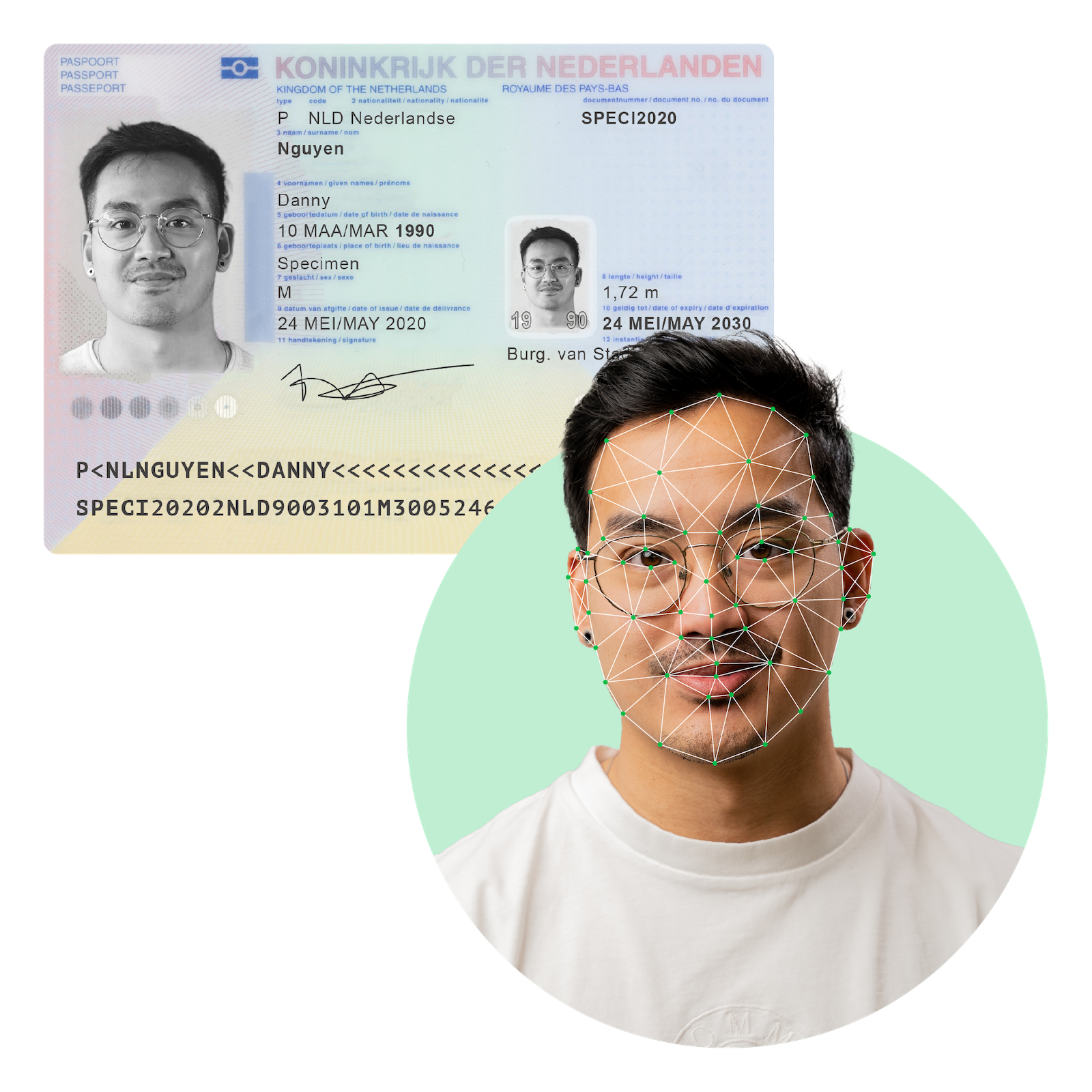
At its core, this method combines low-friction identity validation with strategic risk assessment. It begins with verifying government-issued IDs—such as driver’s licenses or passports—through secure digital scanning and validation tools. These checks confirm authenticity by cross-referencing encrypted data with trusted databases, flagging discrepancies in real time. 3 Surprising Ways ID Documentschain Real Digital Identity Trust
Beyond physical IDs, the approach incorporates behavioral patterns: timing of logins, device fingerprinting, and geographic consistency. These signals create a layered profile, making synthetic or stolen identities far harder to exploit. Unlike rigid, time-consuming manual reviews, this process balances speed and security, improving both user experience and fraud prevention.
By embedding these steps into authentication workflows, organizations reduce false positives, speed up legitimate transactions, and disrupt common fraud tactics—without requiring users to sacrifice convenience.
Common Questions About the Method
Q: Does verifying IDs slow down user login? Modern tools streamline verification through auto-load scanning and AI-driven validation, minimizing wait time. From Scams To Security: Your ID Verification Breakthrough Awaits Most processes take seconds—far less than manual fraud reviews.
Q: Can this method handle international users? Yes, providers design systems to support multiple ID types and regional verification standards, enabling global applicability while adapting to local regulations.
Q: Is it secure enough to combat advanced fraud? When paired with encryption, multi-factor checks, and continuous monitoring, it forms a resilient barrier against identity theft, synthetic profiles, and credential stuffing.
Q: Is this method compliant with U.S. privacy laws? Reputable implementations align with GDPR, CCPA, and state-specific rules, ensuring data handling remains transparent, consensual, and secure.
Opportunities and Realistic Considerations
Adopting this verification method offers clear advantages: reduced chargebacks, stronger customer trust, and better compliance alignment. It’s scalable for small businesses and enterprise platforms alike, requiring only secure integration with minimal training.
However, no method is foolproof. Technical limitations in ID accuracy, regional verification gaps, and evolving fraud techniques demand ongoing updates. Organizations must view this approach as part of a broader security ecosystem—not a standalone fix.
What Scenarios Benefits From Survive Fraud: The ID Verification Method Everyone Overlooks?
This method applies across sectors:
- E-commerce: Reduces fake account fraud and returns by verifying buyer identity. - Financial Services: Prevents account takeover and synthetic identity fraud. - Healthcare Portals: Safeguards patient data access with verified identity confirmation. - Education Platforms: Cuts academic dishonesty risks in online enrollment and proctoring.
It fits both high-risk and routine transactions, making it a versatile tool for risk mitigation.
Common Misconceptions to Clarify
Myth: Verifying IDs always requires physical documents. Reality: Many systems use digital ID photos, biometrics, or third-party trust services that confirm validity without manual processing.
Myth: This method blocks all fraud. Reality: Like any system, it raises the barrier—but vigilance and updated defenses are still necessary.
Myth: It’s only for big corporations. Reality: Mobile-optimized tools make it accessible for small businesses and startups too.
By addressing these myths, users gain confidence in its balance of safety, usability, and real-world effectiveness—key drivers for sustained trust.
Stay Informed—Survive Fraud Is a Journey, Not a Checkbox
The landscape of digital trust evolves daily. What works today may need adaptation tomorrow—especially as fraudsters refine their tactics. Survive Fraud: The ID Verification Method Everyone Overlooks offers a sustainable foundation, turning identity verification from an afterthought into a strategic defense.
For businesses aiming to protect users and preserve credibility, integrating trusted ID checks isn’t optional—it’s essential. For individuals, understanding this method empowers safer digital choices without sacrificing convenience.
In a world where identity theft and fraud tactics grow more sophisticated, staying informed and proactive is your strongest defense. This overlooked method paves the way—not just for survival, but for resilience in an increasingly connected world.