Power Surge In Destruction – Seattle’s Raied-Up Document Shredding Blowback In a year marked by digital transformation and rising concerns over data security, a growing conversation is emerging around an unusual but impactful phenomenon: Power Surge In Destruction tied to Seattle’s heightened focus on aggressive document shredding. What began as quiet local momentum has quickly shifted from niche discussion to mainstream awareness, driven by shifting workplace norms, corporate accountability, and a deeper public focus on protecting sensitive information. This surge reflects real cultural shifts—where data safety, workplace transparency, and reputational responsibility are no longer secondary concerns. 36 KM Through Saklikent: How Long Can You Bear 36 KM To The Canyon?
Why the Power Surge in Seattle’s Document Shredding Practices Is Gaining Traction Following a wave of high-profile privacy disputes and tighter compliance regulations in recent years, Seattle has emerged as a leader in proactive document security. Regional businesses and institutions are responding to growing risks by strengthening shredding protocols—moving beyond simple recycling to secure, traceable destruction methods. This shift reflects broader trends: employees and organizations now prioritize controlling data lifecycle risks, with document destruction no longer just a logistical task but a strategic imperative in safeguarding intellectual property and personal information. Public scrutiny of data misuse, combined with clearer legal requirements, fuels this transformation.
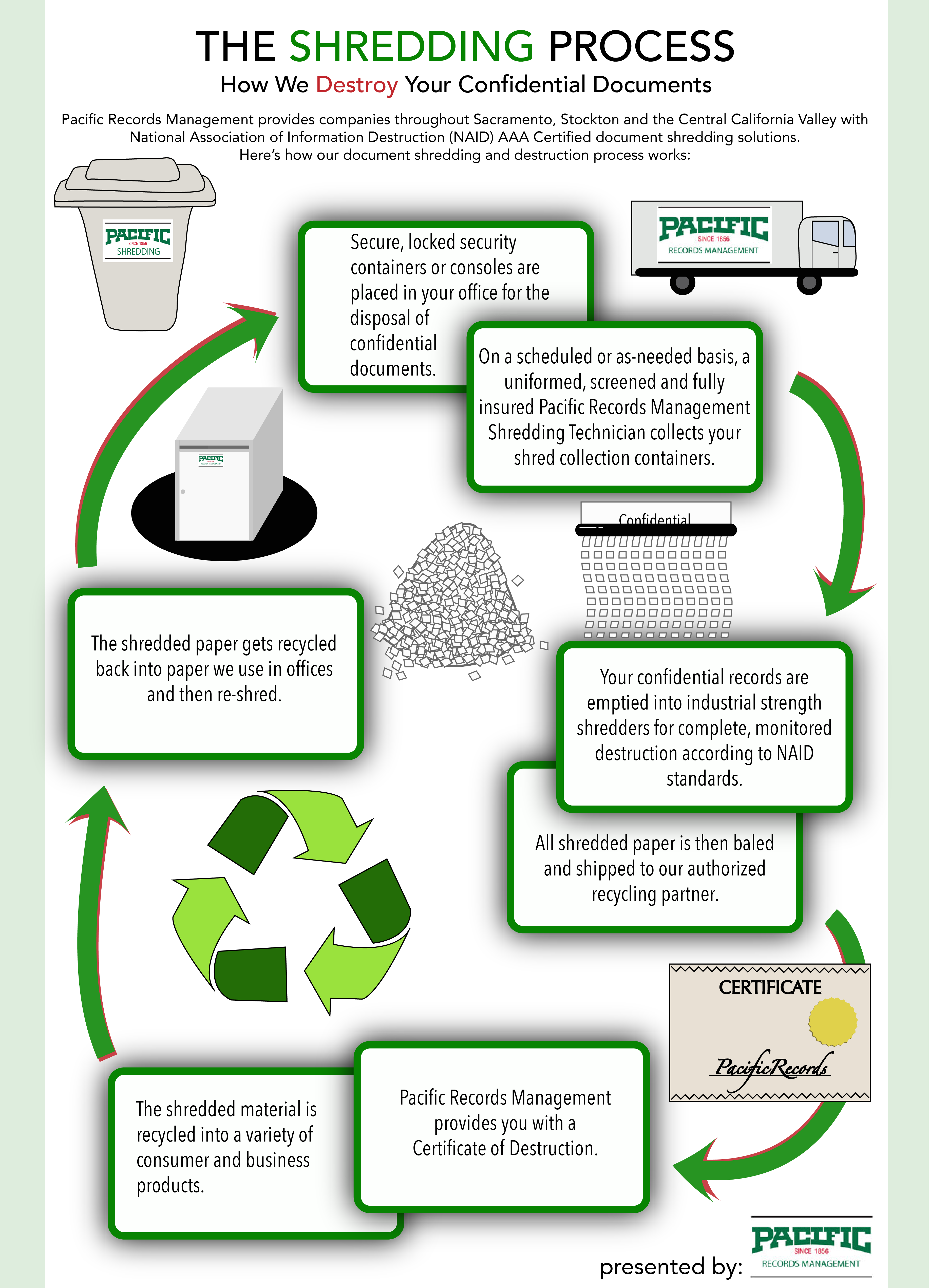
How these new shredding practices work is rooted in accessibility and rigor. 36 KM Through Saklikent: How Long Can You Bear 36 KM To The Canyon? Unlike basic shredding, the Seattle-driven approach blends secure digital wiping with physical destruction, often incorporating chain-of-custody tracking. This hybrid model ensures accountability—critical in industries where document integrity directly affects compliance and trust. The rise of this system underscores a quiet but powerful message: organizations and individuals are no longer passive about data exposure but actively managing its end-of-life through precise, monitored methods.
How Document Shredding Blowback Is Building Momentum in Public Discourse The phrase Power Surge In Destruction captures more than literal blade action—it reflects a cultural reset around information control. Seattle’s local increase in robust shredding practices has sparked broader debate on how sensitive data is handled across the U.S., particularly as more companies adopt similar standards. 36 KM Through Saklikent: How Long Can You Bear 36 KM To The Canyon? This attention stems from a confluence: greater awareness of identity theft, stricter state-level privacy laws, and a public increasingly aware that discarded documents still pose security risks. News coverage, industry panels, and workplace forums now treat paper destruction as a frontline defense—drawing public interest and driving demand for verified solutions.
This growing visibility raises important questions: How reliable are current methods? Who benefits most? And what real value does a structured shredding strategy bring? The answers lie not in hype, but in measurable benefits: reduced liability, enhanced regulatory compliance, and peace of mind. As more communities learn about the power behind responsible document destruction, conversations are shifting from anecdotal concern to informed action.
Common Questions About Power Surge In Destruction – Seattle’s Document Shredding Blowback
How secure is modern document shredding? Today’s shredding techniques combine digital data wiping with certified physical destruction. Most systems use industrial-grade cross-cut or micro-cut shredders that reduce documents into unrecoverable fragments. With documented chain-of-custody logs, these processes provide verifiable proof of secure disposal—critical for organizations needing audit-ready compliance.
Why isn’t just recycling enough anymore? Even heavily scribbled or printed files retain identifiable patterns, metadata, and digital traces. Beyond environmental concerns, improperly shredded documents enable identity theft and data breaches. Proactive shredding closes these risks at the source.
What kind of organizations should prioritize stronger shredding? Businesses in healthcare, finance, legal services, and education face high data volumes and strict compliance standards. But individuals handling sensitive personal records—tax files, medical records, legal documents—also benefit from structured destruction protocols.
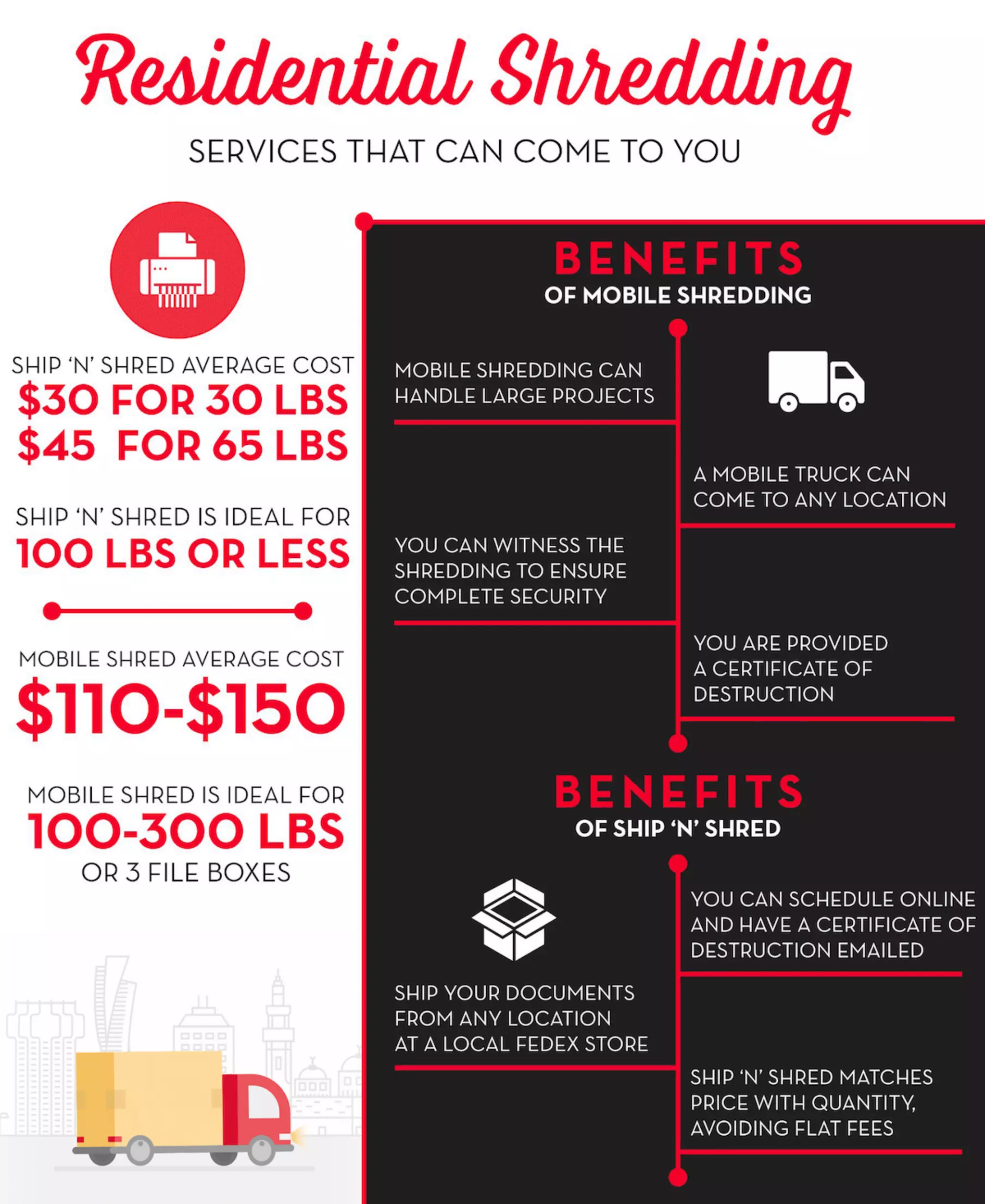
Is the Seattle model realistic at a smaller scale? Yes. The principles—auditable tracking, layered destruction, and employee education—apply regardless of size. Even small companies can adopt professional-grade services or secure in-house systems with traceable reports to ensure reliability.
How do I verify my shredding provider’s trustworthiness? Look for third-party certifications like NAID AAA certification, which guarantees secure handling and disposal. Reputable providers offer digital receipts, audit logs, and customer testimonials to verify performance.
Who Benefits Most from Document Shredding Blowback Trends? From compliance officers securing enterprise data to remote workers handling home records, the movement supports anyone handling sensitive material. It gives organizations a proactive edge in risk management while empowering individuals to protect personal privacy with confidence.
Opportunities and Considerations The rise of structured document destruction presents clear advantages: reduced legal exposure, improved data governance, and stronger stakeholder trust. Implementing these practices requires upfront effort—choosing a certified service, training staff, and establishing clear protocols. While not a standalone security solution, it’s a vital layer in a comprehensive data protection strategy. Organizations should view it as part of an ongoing commitment rather than a one-time task, adapting methods as regulations evolve.
What People Often Misunderstand About the Shredding Blowback A common belief is that any shredding adequately protects data—but that’s not true. A chaotic or opaque process leaves gaps. Another myth: digital wiping alone ensures safety, yet data stored on hard drives or cloud backups can be recovered without certified destruction. The truth is, security starts at the end of a document’s life—and how it’s disposed defines actual protection.
Who Should Consider Embracing This Trend? Anyone processing sensitive information—small businesses, remote teams, legal professionals, educators, and household managers—stands to gain. As awareness grows, those delaying action risk higher vulnerabilities. Taking early, informed steps builds resilience and keeps pace with rising expectations around digital responsibility.
Soft CTA: Take Control of Your Data Lifecycle The Power Surge In Destruction isn’t about destruction for shock—it’s about control, accountability, and foresight. Stay informed. Assess your document security. Small, intentional steps today lay the foundation for safer, compliant tomorrows. Explore secure shredding solutions, ask your provider about traceable protocols, and make sure every paper you dispose of is fully protected. Knowledge is your first defense.