Hidden Rules Of ID Verification You Must Know To Avoid Blocked Access
In today’s digital landscape, seamless access to online services is a daily necessity—yet getting blocked at login or account setup often surprises even the most tech-savvy users. Behind the scenes, subtle but powerful rules govern how identity verification works, shaping who gets through without friction and who triggers automatic security alerts. Understanding these “hidden rules” isn’t just about avoiding lockouts—it’s about preserving access, trust, and opportunity in a world where digital identity is increasingly monitored. Step 1 To Trust: Why ID Document Verification Must Be Flawless This article explores the key principles of ID verification that influence access—and why staying informed can make all the difference.
Why Hidden Rules Of ID Verification You Must Know To Avoid Blocked Access Are Gaining Attention in the US
Public concern around secure digital onboarding is rising across the United States, driven by growing awareness of identity fraud, account takeovers, and evolving regulatory standards. As businesses tighten verification protocols to protect user data and comply with federal guidelines, many experience unexpected access blocks—often without clear explanations. Social media and news cycles highlight stories of legitimate users locked out, fueling curiosity about what’s really happening behind the scenes. Step 1 To Trust: Why ID Document Verification Must Be Flawless Meanwhile, emerging technologies and tighter data policies mean traditional login methods are being re-evaluated, increasing the need to decode subtle triggers that determine success or denial during identity checks.
How Hidden Rules Of ID Verification Actually Work
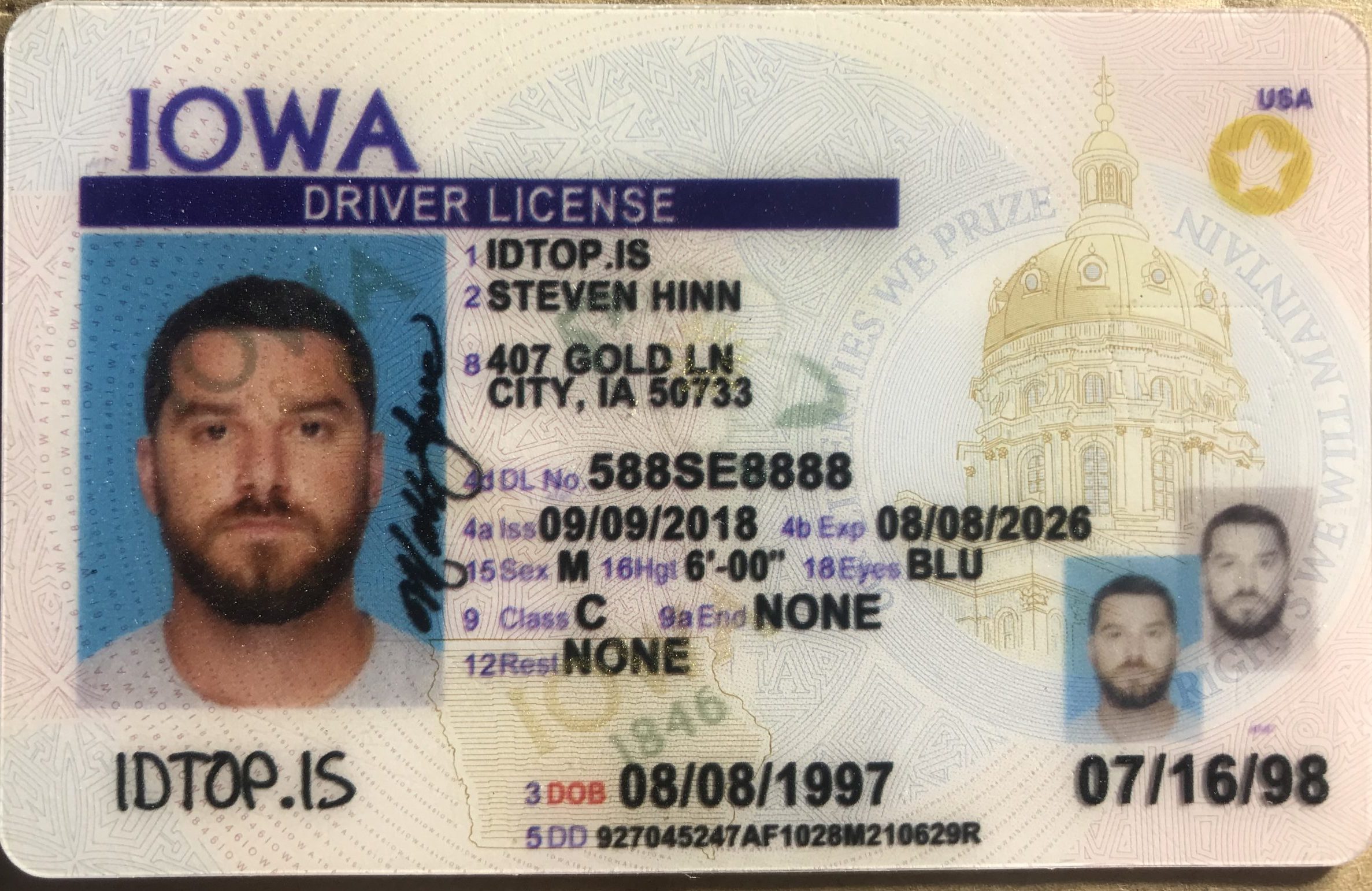
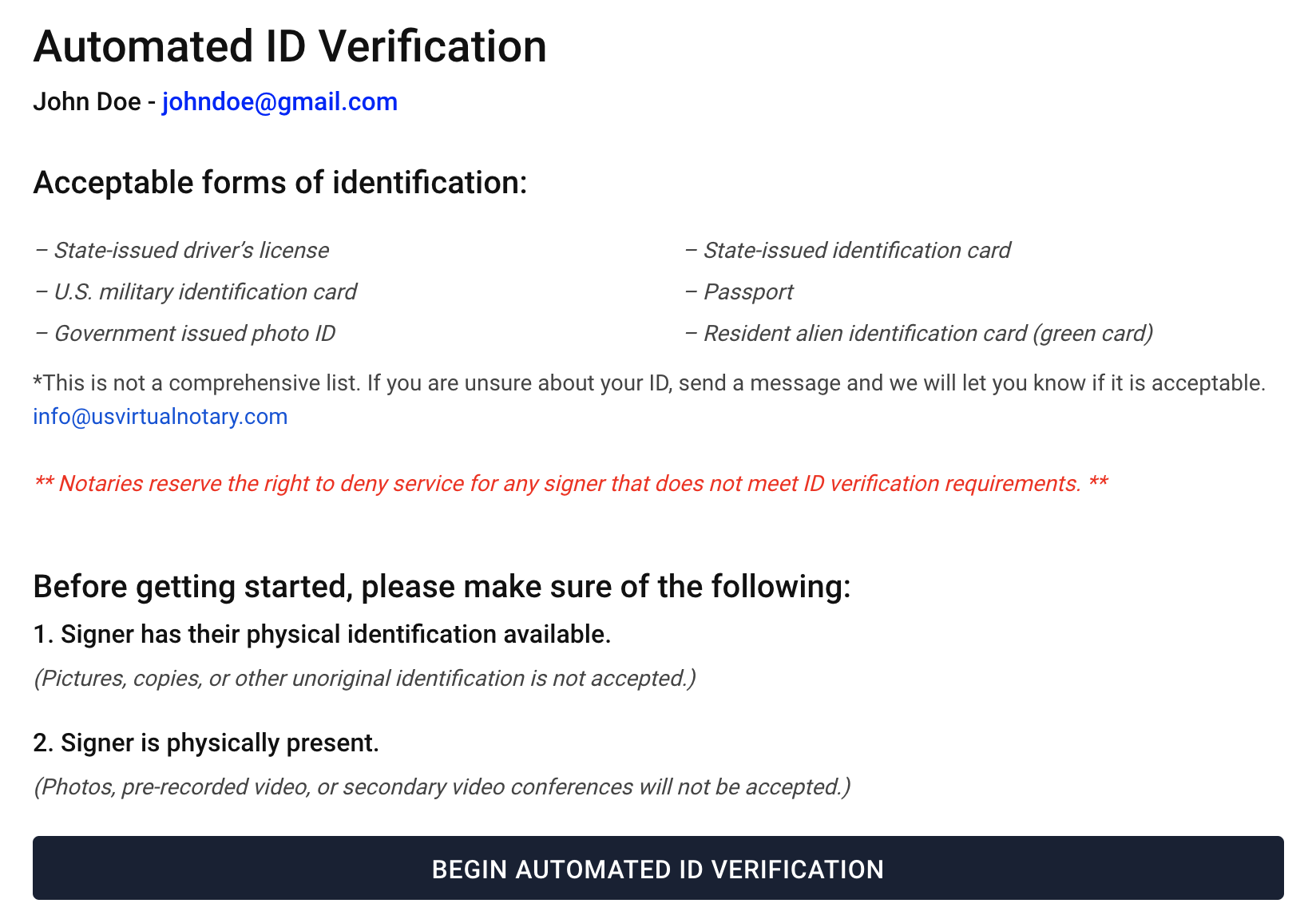
At its core, identity verification balances security and usability. Platforms rely on layered checks—ranging from document validation to biometric matching—designed to confirm a real person’s identity without excessive friction. Critical but often unnoticed elements include: - Matching data consistency across submitted forms and official records - Behavioral patterns like typing speed, device fingerprinting, and login timing - Risk-based triggers activated by anomalies such as sudden location changes or bulk access attempts None of these alone block access, but combined, subtle inconsistencies or environmental cues can prompt verification challenges like two-factor prompts or AI-assisted reviews. This nuanced process keeps systems secure while preserving legitimate access. Step 1 To Trust: Why ID Document Verification Must Be Flawless
Common Questions People Have About Hidden Rules Of ID Verification You Must Know To Avoid Blocked Access
- What triggers automatic identity block? Not every unusual login is suspicious. Platforms analyze risk signals—such as mismatched biometrics, rapid failed attempts, or use from unfamiliar devices—to decide when extra verification is needed.
- Why do I get a CAPTCHA or code after valid info? These steps act as dynamic safeguards, confirming the user is human rather than bot-based access. They’re part of layered security, not a random hurdle.
- How does location affect access? Access patterns tracked via IP location help detect unauthorized logins. Survive Fraud: The ID Verification Method Everyone Overlooks A sudden shift from a known region to a different country may trigger extra steps.
- Can temporary or shared credentials violate verification rules? Shared access codes or pre-issued tokens may fail identity checks, especially if not tied to verified identity claims. Rules often require unique, personally linked credentials.
- What happens if I get blocked? Most platforms allow appeals or refreshed verification steps. Clear communication from service providers helps resolve issues quickly.
Opportunities and Considerations
Understanding these rules empowers users and organizations alike to navigate digital spaces more confidently. On the plus side, informed users save time by avoiding common pitfalls—like mismatches in official documents or outdated credentials—reducing false rejections. Businesses benefit from smarter systems that cut fraud while preserving customer trust. Yet, no method is foolproof. Overly aggressive verification can inconvenience legitimate users, and complex rules may create confusion. Realistic expectations—knowing blocks often signal security, not error—help maintain patience and cooperation.
Things People Often Misunderstand About Hidden Rules Of ID Verification You Must Know To Avoid Blocked Access
A frequent misconception is that getting blocked means identity fraud is confirmed—yet most systems rely on risk assessment, not guilt confirmation. Another myth is that multiple failed attempts always trigger immediate lockouts; in reality, platforms often use delay penalties instead of instant blocks. Misunderstanding also fuels frustration when shared access or temporary credentials fail verification. Clear education around these nuances builds trust and reduces unnecessary anxiety in a space where confusion runs high. 3 Surprising Ways ID Documentschain Real Digital Identity Trust
Who Hidden Rules Of ID Verification You Must Know To Avoid Blocked Access May Be Relevant For
These principles touch diverse groups: remote workers juggling international access, small business owners managing customer onboarding, gig workers relying on platform accounts, and students accessing digital learning portals. Frequent travelers, frequent logins, and individuals from underrepresented regions face greater verification complexity due to data fragmentation and regional risk profiles. Regardless of use case, staying aware of subtle indicators preserves uninterrupted access and digital identity freedom.
Soft CTA: Stay Informed and Empower Your Digital Access
Knowing the hidden rules of ID verification isn’t just about avoiding blocks—it’s about staying in control. Stay curious, verify your info regularly, and explore secure self-service tools to strengthen your digital presence. Empower yourself by understanding what enables smooth access and what might trigger a pause—because awareness today builds confidence tomorrow.






![[4 Ways] How to See Blocked Numbers on Your iPhone 2024](https://www.mobitrix.com/apple-support/images/article/en/find-blocked-numbers-on-iphone.png)