From Scams To Security: Your ID Verification Breakthrough Awaits
In an era where digital interactions happen faster than ever, a quiet crisis persists: credential theft and identity fraud are rising, with millions of Americans unwittingly caught in scams that exploit weak ID verification systems. The digital landscape grows more complex by the day, and trust in online services hinges on one critical foundation: secure identification. That’s why From Scams To Security: Your ID Verification Breakthrough Awaits is emerging as a vital focus for anyone seeking safer digital experiences without sacrificing convenience. 3 Surprising Ways ID Documentschain Real Digital Identity Trust
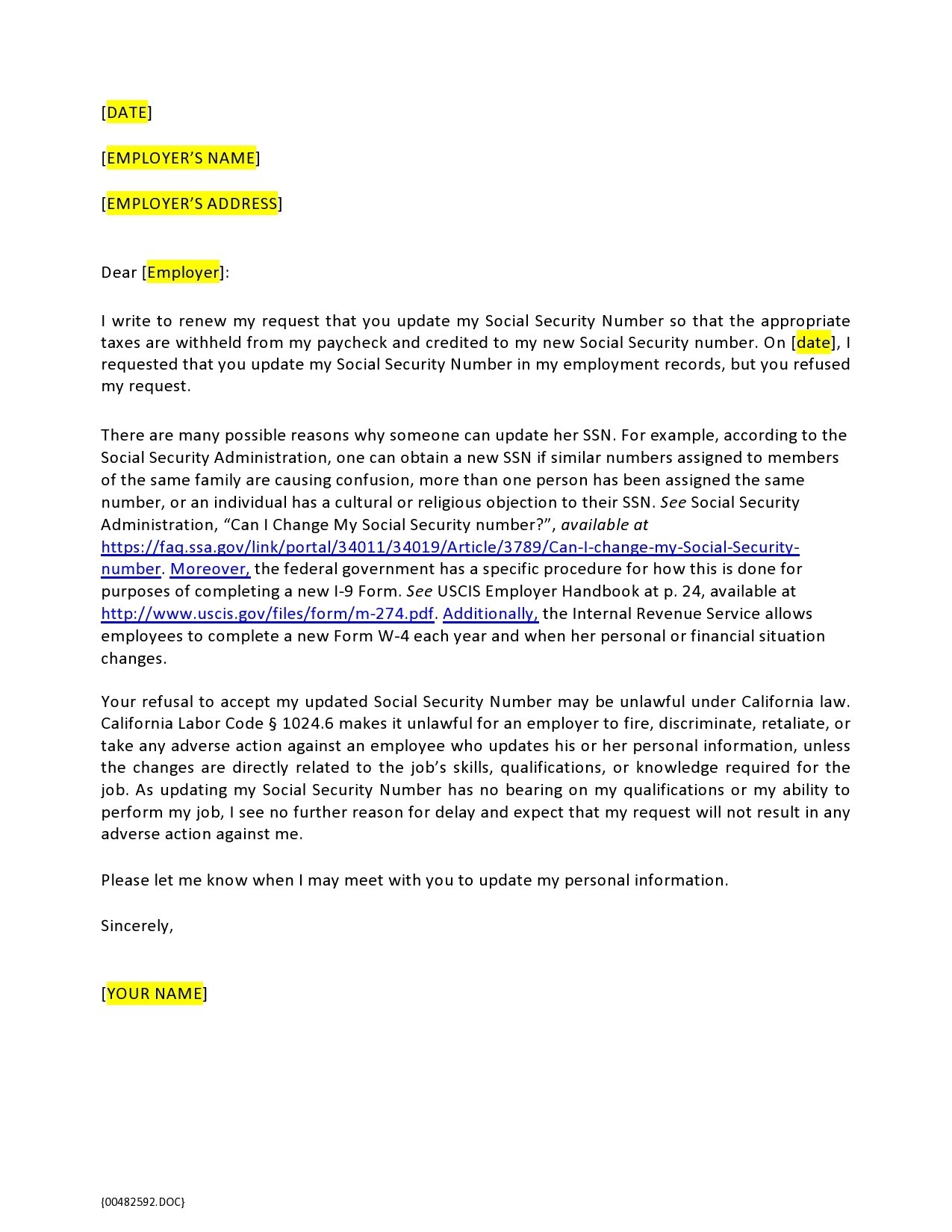
People are increasingly aware that traditional verification methods—like static passwords or basic security questions—are no longer enough. Scammers have grown more sophisticated, exploiting gaps in identity validation across fintech, healthcare, and government platforms. The demand for smarter, faster, and more reliable verification is no longer a niche concern—it’s becoming essential for personal and financial security across the U.S. market.
What’s changing? Breakthroughs in biometric authentication, AI-driven fraud detection, and decentralized identity solutions are reshaping how we protect sensitive data. 3 Surprising Ways ID Documentschain Real Digital Identity Trust These tools are not only stronger against deception but also reduce friction for legitimate users. The movement toward “secure identity by design” reflects a broader shift: identity verification is no longer a one-time hurdle but a continuous process built on trust, resilience, and real-time validation.
How From Scams To Security: Your ID Verification Breakthrough Awaits Actually Works
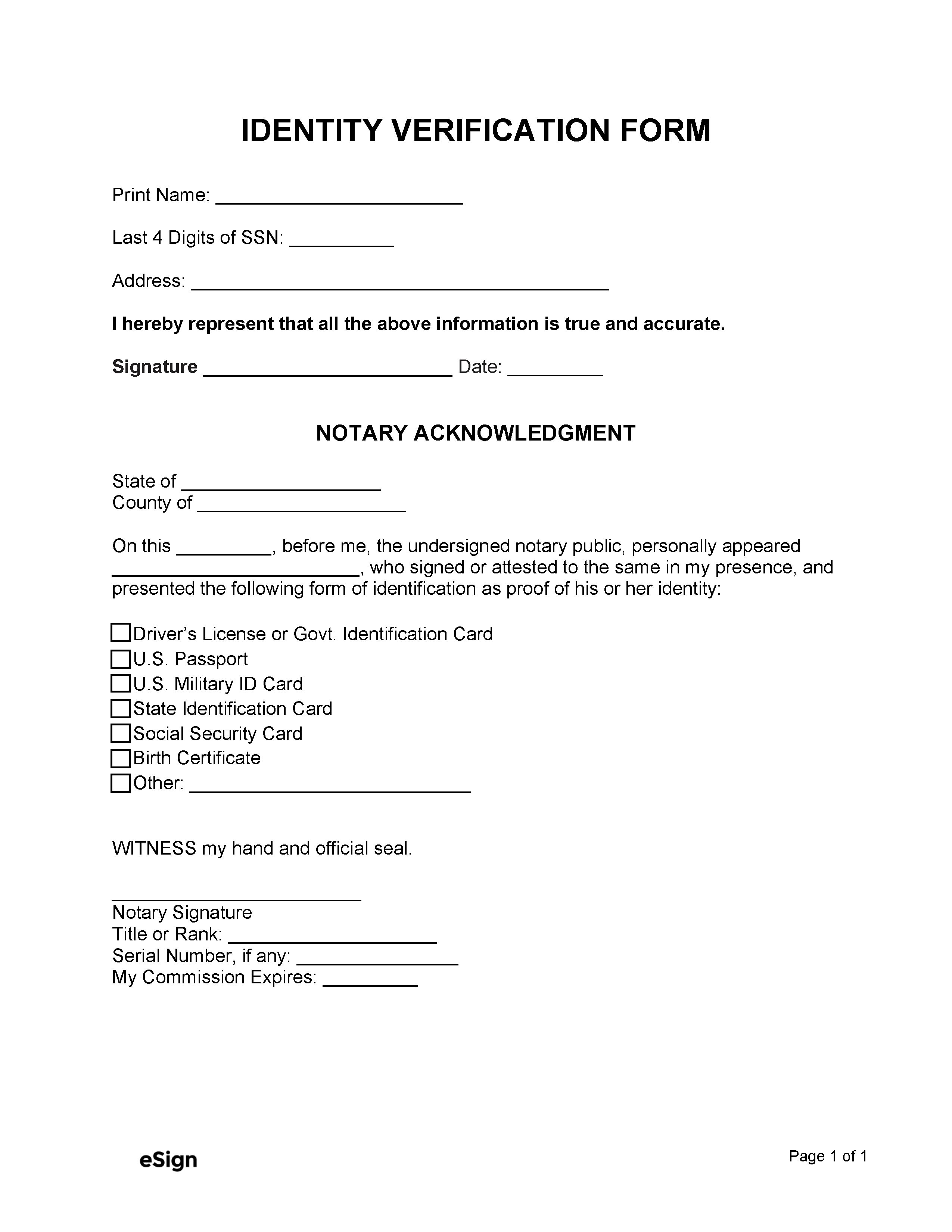
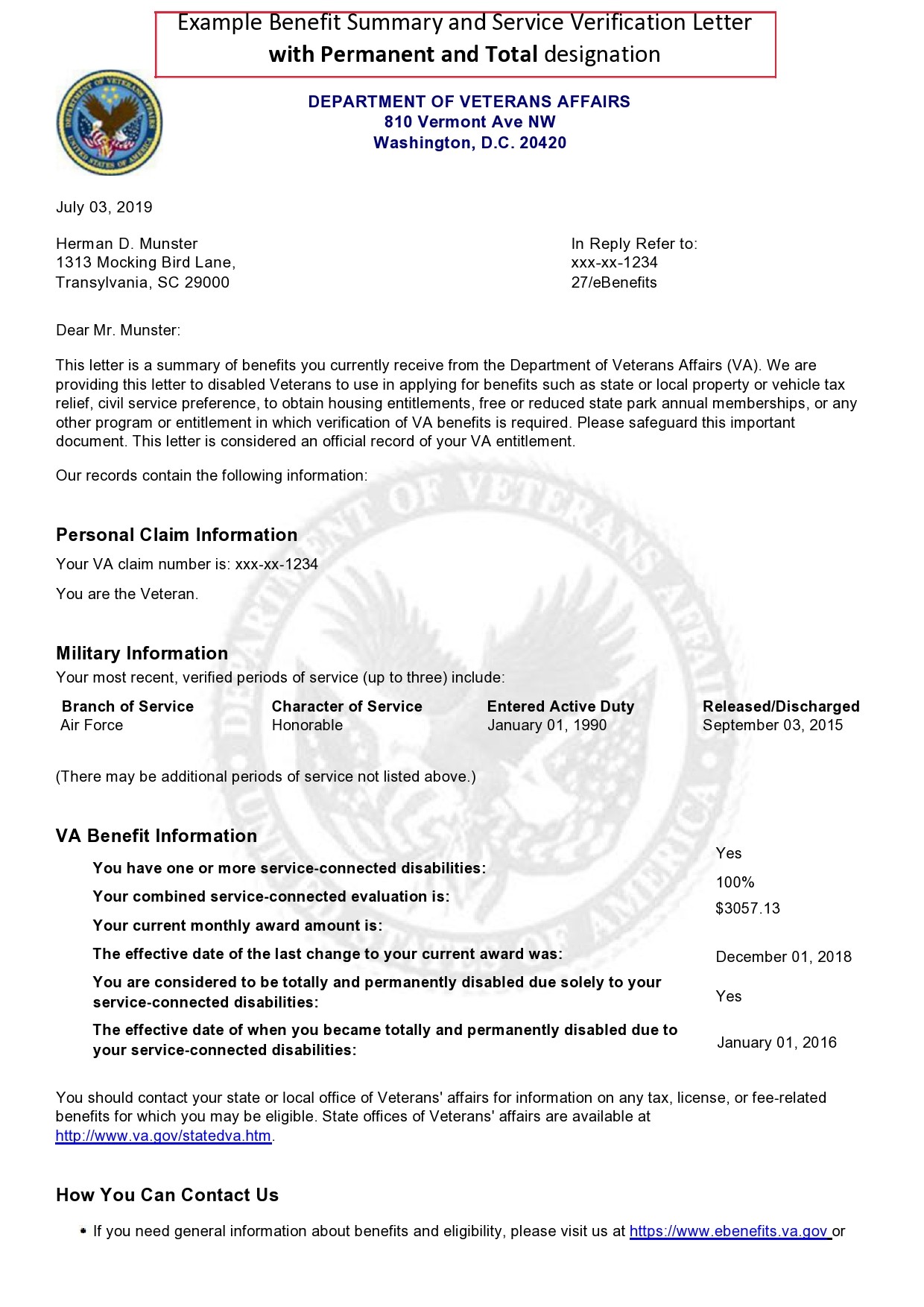
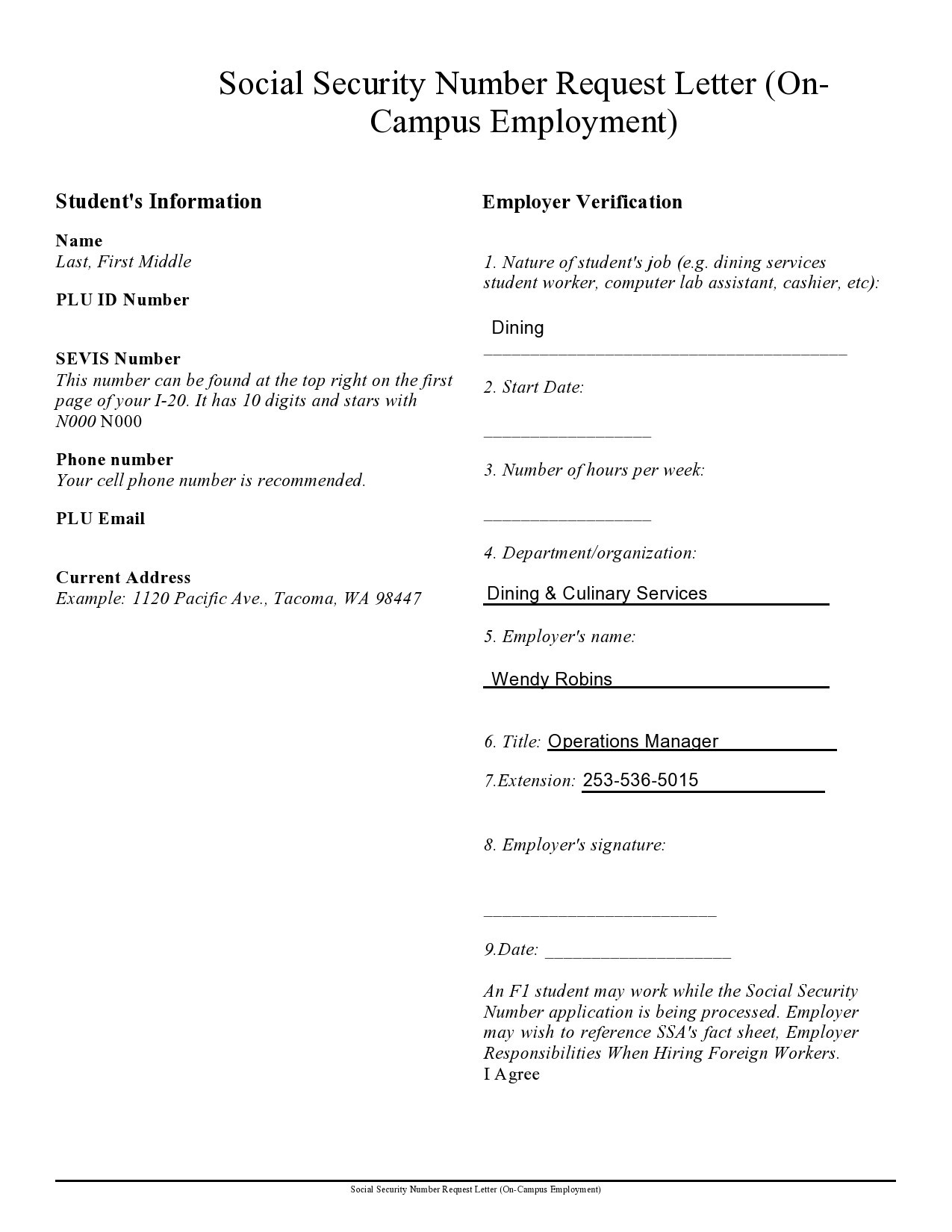
At its core, this breakthrough relies on moving beyond passwords and static answers. Modern verification systems now integrate multiple layers of identity proof—such as facial recognition, document scanning with liveness detection, and behavioral analytics—creating a seamless yet robust security net. 3 Surprising Ways ID Documentschain Real Digital Identity Trust These tools authenticate users based on unique biological traits and real-time behavior patterns, making spoofing nearly impossible for bad actors while remaining user-friendly.
Mobile-first platforms are adopting these innovations at scale, recognizing that trust begins with a single, secure verification step. Whether signing into healthcare portals, opening a mobile bank account, or accessing government services, users now experience faster onboarding without compromising safety. Behind the scenes, machine learning models continuously adapt to new fraud tactics, ensuring systems evolve as threats grow more complex.
Common Questions People Have About From Scams To Security: Your ID Verification Breakthrough Awaits
How safe is this new verification process? Unlike outdated methods, modern systems employ multi-factor checks that adapt to real-time risks. Liveness detection ensures photos or recordings aren’t used, reducing spoofing. Combined with encrypted data storage, this creates a layered defense against identity theft.
Does this affect privacy? Reputable solutions prioritize privacy by design—only essential data is processed, with strict controls on storage and sharing. Users retain ownership and control over their verified information, aligned with growing data protection standards.
Is it accessible for everyone? Yes. Innovations now aim to reduce barriers across demographics, including accessibility features for users with disabilities or limited tech literacy. Efforts focus on simplicity without sacrificing security.
How long does verification take? Most systems complete authentication in under 60 seconds on mobile devices—fast enough to keep users engaged without frustration. Speed and safety go hand in hand.
Will this eliminate scams entirely? No system is perfect, but breakthroughs make successful fraud exponentially harder. When paired with user education and proactive monitoring, these tools form a powerful shield against identity abuse.
Opportunities and Considerations
The shift toward advanced identity verification offers clear advantages: stronger protection, reduced financial losses, and increased confidence in digital transactions. For small businesses and large platforms alike, implementing these systems can enhance trust, improve compliance, and lower fraud-related costs.
Still, adoption requires awareness. Users must understand that verified ID processes are not about surveillance but security. Companies need transparent communication about how data is used. Balancing innovation with ethics remains key. Why Delayed ID Verification Costs You More Than You Think
Who From Scams To Security: Your ID Verification Breakthrough Awaits May Be Relevant For
From streamlining account sign-ups to securing sensitive healthcare records, this progress matters across contexts. It benefits anyone handling online identities—from first-time app users to established organizations managing client data. Not just for fintech or e-commerce, but for government services, remote voting initiatives, and digital government IDs gaining traction nationwide.
Even those concerned with digital inclusion will find value—systems designed to be accessible help bridge gaps, ensuring safer access for all while building collective resilience.
Things People Often Misunderstand
- Myth: Advanced verification slows down service access. Your Fastest Path To Verified Identity×Inside The Document Proof System Fact: Modern systems optimize for speed; delays are rare and minimal, especially on mobile devices.
- Myth: My data is shared freely with third parties. Fact: Legitimate verification uses encrypted, on-device processing with minimal data sharing, aligned with strict privacy laws.
- Myth: It’s only for high-risk platforms. Fact: Security layers are valuable across all digital interactions, enhancing trust universally.
- Myth: It replaces traditional passwords entirely. Fact: It often replaces passwords altogether or strengthens them with additional layers, making reused credentials obsolete.
Soft CTA: Stay Informed, Stay Protected
The future of safe digital identity is unfolding—secure verification awaits not just as a response to scams, but as a foundation for trust in an evolving online world. By staying informed, choosing trusted platforms, and engaging with reliable tools, users and organizations alike can turn awareness into action. No single solution ends scams, but ongoing innovation brings us closer to a digital environment where security and convenience coexist—making “From Scams To Security: Your ID Verification Breakthrough Awaits” more than a promise, increasingly a reality.