Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force What is behind the growing curiosity about this digital secret door?
In a climate where digital boundaries blur and curiosity about hidden access grows, Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force has emerged as a recurring topic across mobile-first platforms in the US. Users increasingly seek explanations for platforms and passwords offering entry to exclusive, intense, or otherwise restricted digital spaces—spaces that feel both alluring and out of reach. Break Into Helloid Login: Decoding The Hidden Power Ready Waiting For You This underground interest reflects broader trends: a desire for deeper digital immersion, skepticism toward conventional interfaces, and emerging patterns around niche online identity.
This article demystifies what Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force represents—not through explicit claims, but through informed insight. We explore how this concept operates, clarify common misconceptions, and consider where it may matter. Designed for mobile readers seeking authentic answers, the content encourages mindful engagement without exploitation.
---
Why Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force Is Gaining Attention in the US Break Into Helloid Login: Decoding The Hidden Power Ready Waiting For You
Digital communities today thrive on mystery and exclusivity. The rise of password-powered portals, niche platforms, and access-based interfaces signals a shift: users value scarcity and secure identity verification more than ever. Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force reflects this evolution, with growing discussion around tools and accounts granting entry to digitally sealed environments.
While the phrase itself resonates more as a cultural signal than a literal product, its traction mirrors broader trends: users report heightened curiosity about hidden digital realms, driven by digital fatigue, a search for authenticity, and demand for personalized online experiences. This moment is defined by growing skepticism toward open-access platforms and parallel interest in secure, curated access. Break Into Helloid Login: Decoding The Hidden Power Ready Waiting For You
---
How Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force Actually Works
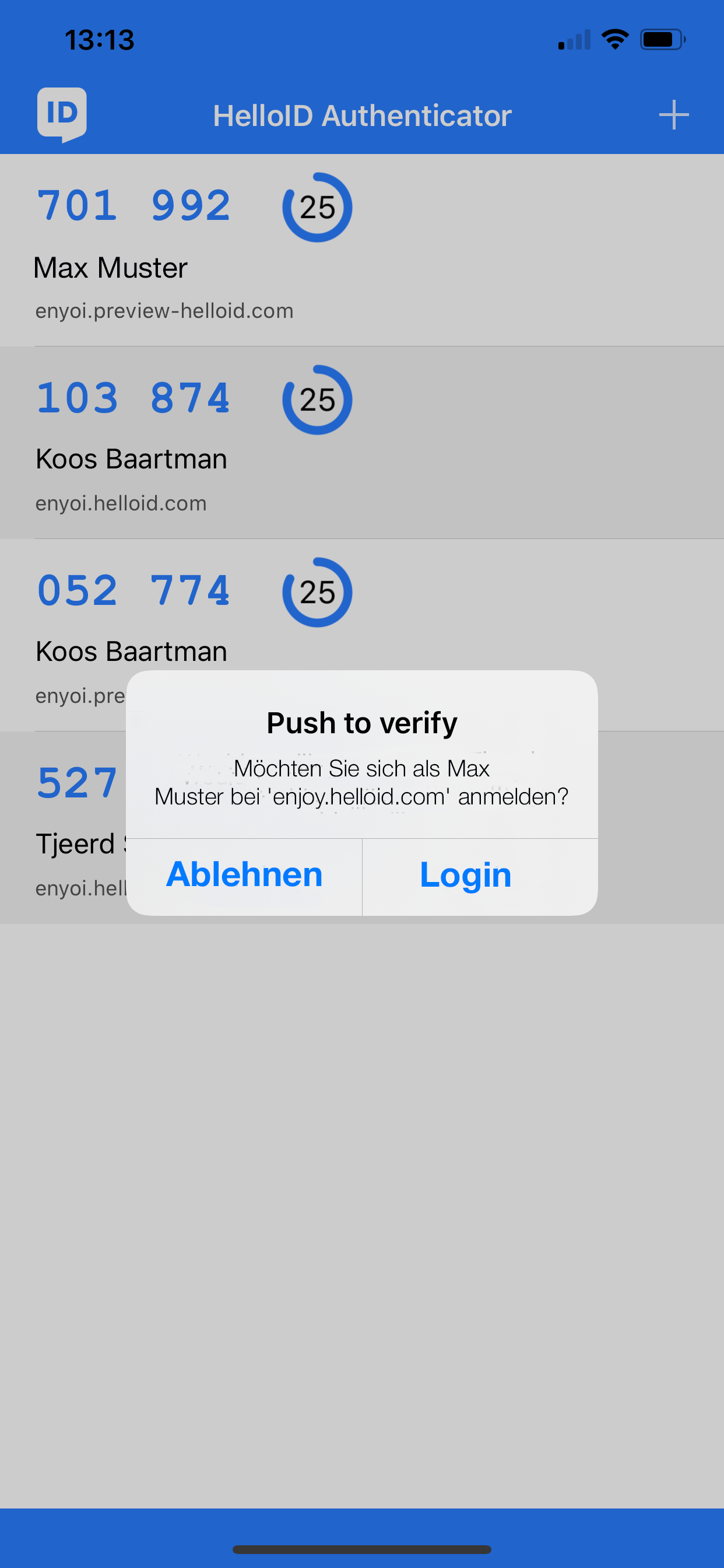
The concept relies on cryptographic or behavioral triggers—often unique identifiers or master access keys—that unlock restricted pages, apps, or networks behind layers of authentication. Unlike conventional logins, “forbidden access” implies systems guarded by custom protocols: pattern-based entry, biometric validation, or tokenized verification hidden from standard interfaces. From Mystery To Power: The Hidden Fire Behind Helloid Login Login Fast
Users gain entry through carefully constructed methods—such as mastering obscure commands, sharing verified keys within trusted circles, or exploring open-source tools designed to bypass conventional gateways. These are not shortcuts but deliberate, skill-based pathways requiring awareness and patience.
Functionally, this refers to digital environments where access is granted selectively, often by design to protect privacy or create exclusive engagement. The mechanism itself is not inherently explicit; rather, it represents a growing layer of digital identity control accessible to informed users.
---
Common Questions People Have About Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force
Q: Is “Forbidden Access” illegal or unsafe? A: No. The phrase refers to restricted access—legal systems, paid services, or private platforms requiring special credentials. These tools are not illegal, but users should remain cautious of unverified sources.
Q: How do I gain access? Last Chance: Unlock Helloid Login With This Untapped Power Before It Vanishes A: Legitimate access often comes via invite-only networks, password-protected portals, or authorized keys shared within trusted communities. There are no known safe shortcuts—authentication requires effort and trust.
Q: Can this access harm my device or data? A: When obtained through verified, developer-sanctioned methods, the access is secure. Risks arise from scams or phishing—always verify sources before sharing credentials.
Q: Is this just a social media gimmick? A: Not entirely. While some platforms use the concept for identity innovation, Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force symbolizes a broader shift toward exclusive, permission-based digital experiences that demand user awareness.
---
Opportunities and Considerations
Pros: - Encourages digital literacy and critical thinking about trust - Supports development of secure, user-controllable platforms - Matches growing consumer demand for privacy and exclusivity
Cons: - Risk of misinformation spreading in unregulated spaces - Potential for scams targeting curious users seeking entry - Limited mainstream availability—requires active exploration
Realistic expectations hinge on patience and responsible engagement: this access is not instant, nor universal. It serves niche communities rather than the general public.
---
Who Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force May Be Relevant For
This concept appeals primarily to tech-savvy users exploring identity control, indie creators building exclusive communities, privacy-conscious professionals, and digital ethnographers studying access culture. While not a mass-market offering, it speaks to evolving US digital behaviors—especially among younger, mobile-first audiences questioning how and where power lies beneath surface-level interfaces.
---
Soft CTA: Explore, Inform, Stay Curious
Understanding Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force invites users to think deeper about digital boundaries and personal control. Rather than rush to access, take time to explore reputable sources, learn about authentication systems, and consider what authenticity means in a digital age defined by exclusivity and guardrails.
Remaining informed is your strongest access—always verify, protect your data, and engage with purpose.
---
Conclusion
Forbidden Access UnveiledLog Into Helloid Powered By A Secret Force isn’t a single product or a secret code—it’s a lens through which growing curiosity about secure, intentional digital entry is being explored. In a fast-moving landscape shaped by privacy, identity, and boundary-pushing innovation, this trend reflects a desire for more mindful access.
By approaching the concept with curiosity, critical thinking, and responsible engagement, readers transform from passive observers into informed explorers—bridging mystery with meaning, one verified step at a time.