1 Power Word Login Hack Revealed In Id Environment Gains Focus in US Digital Landscape
What powers seamless access to increasingly secure digital spaces without friction? In today’s fast-moving, privacy-conscious world, users are not just seeking convenience—they’re demanding intelligent, frictionless login experiences. Heat Pump Fail Fast Pays Off×Seattle's Fast Repair Solution Wait Time Zero The phrase “1 Power Word Login Hack Revealed In Id Environment” is no longer a niche curiosity but a signal of a tangible shift toward smarter authentication methods. As digital identity management evolves, this simple yet powerful concept is capturing attention across the US, driven by growing concerns over security, speed, and user control.
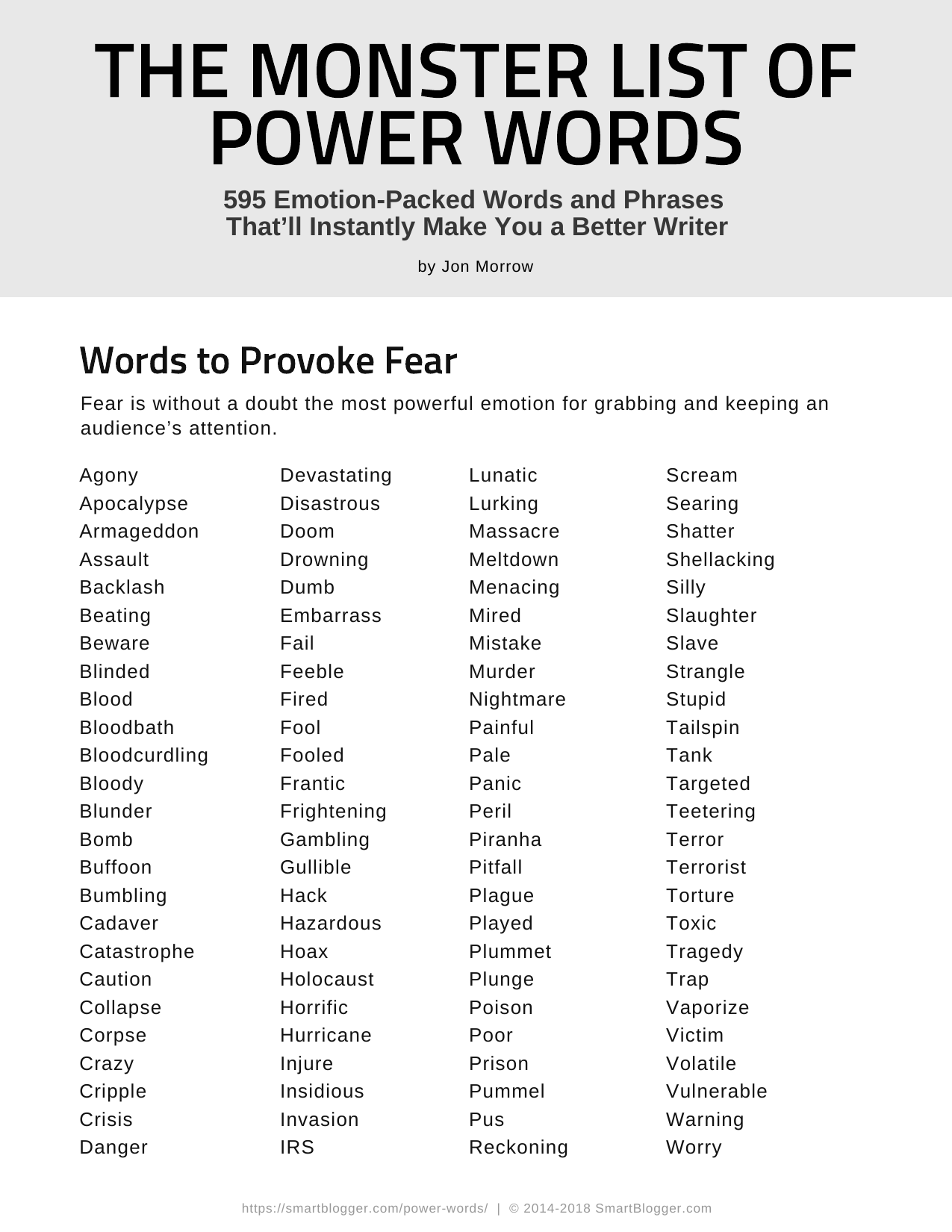
This login strategy centers on leveraging a single, strategic phrase—or “power word”—to unlock streamlined access, reduce credential fatigue, and enhance environment-based authentication. Far from magic, it’s a thoughtful integration of identity verification principles and user experience design, especially relevant as digital identity becomes more context-sensitive and environment-aware.
In the United States, where online trust and privacy are high-priority concerns, users are increasingly wary of complex or repetitive login efforts. Heat Pump Fail Fast Pays Off×Seattle's Fast Repair Solution Wait Time Zero Security breaches and data exposure make every touchpoint critical. This login hack offers a practical solution: using a carefully chosen word or phrase tied to user identity and digital context allows quicker, safer access—aligning with modern expectations for efficiency and personal control.
How does this “Hack” work in practice? At its core, it relies on contextual authentication—matching a user’s behavior, device, and identity to streamline entry. The power word acts as a lightweight signal: a trusted identifier linked to verified credentials, enabling frictionless access without sacrificing security. Heat Pump Fail Fast Pays Off×Seattle's Fast Repair Solution Wait Time Zero This method works especially well in environments that recognize repeated, authorized use—such as trusted apps, corporate systems, or member portals—where identity context strengthens both convenience and protection.
Not every login method suits every user. Some may find the phrase confusing or suspicious, especially without transparency around how it works. This is why it’s vital to understand the real and safe applications of this approach: it enhances access control but requires responsible implementation with clear user expectations.
Common questions arise around authenticity, privacy, and security. Does using a single word weaken protection? Not when paired with modern encryption and multi-factor safeguards. Can it lead to misuse? Only if implemented without proper safeguards. The key is awareness: this trick is not a bypass, but a support mechanism designed to align with user behavior while strengthening digital identity management.
Different users benefit in distinct ways. Students managing course portals, professionals accessing secure workspaces, parents accessing family apps—each finds unique value in login friction reduced through intelligent context recognition. Yet expectations must remain grounded: this is a tool, not a shortcut. Real results come from thoughtful adoption within secure systems.
Misconceptions abound—some fear it’s a vulnerability or a loophole. The truth is more nuanced. When properly integrated, it reinforces identity checks in smarter ways, reducing annoyance while raising security standards. Users should see it as a partner in safer digital habits, not a risk.
Who should pay attention? Anyone invested in identity-first technology: users seeking smoother access, enterprises protecting sensitive data, and digital service providers building trust. This approach fits naturally into environments where user context matters—responsive login by device, trusted network identification, or adaptive authentication based on behavioral patterns.
The path forward lies in clarity and cautious adoption. Embrace education, not clickbait. Understand the balance between convenience and security. Stay informed about how login systems evolve—not just in tech, but in culture and regulation.
In a world where digital identity grows more complex, the “1 Power Word Login Hack Revealed In Id Environment” emerges as a quiet yet powerful shift—toward smarter access, greater control, and smarter trust. It’s not about bypassing security, but enhancing it—with intention, context, and care. As users and systems progress, this simple phrase illuminates a clearer, more secure digital path forward.






.png)
